The need for e-commerce payment security is something that you cannot brush off.
Although every year has witnessed e-commerce fraud since 1993, recent years have noticed a worrying trend.
According to the Juniper Research, the period between 2018 and 2024 may witness increased card-not-present frauds costing online businesses $130 billion.
Every serious business should rush to close doors through which payment frauds occur. Engaging the services of security solutions can save you from a lot of headaches.
So, which are some e-commerce payment security issues that your business can face?
Which e-commerce payment security steps can you take to stay safe? We have you covered in this article.
Excited, lets jump right into the list.
Types Of E-commerce Payment Hacks and Frauds
Hackers have thousands of ways to hacks into others system but these are the common types of e-commerce online payment frauds use.
Payment gateways online have never been so convenient.

1. True fraud/Identity theft fraud
The bad players take on the identity of a victim, use the person’s name to create credit cards, and shop online using the fraudulent cards.
As the scope and number of data breach skyrocket, we are noticing a rapid increase in this type of fraud.
Given the sophisticated nature of these fraudsters, this type is one of the most challenging.
2. Chargeback or friendly fraud
A buyer will purchase an item or service. After delivery, they issue a chargeback with a claim that someone stole their card.
Such culprits are mostly clients who want to get the products for free with a fraud. Although it’s difficult to detect, you can win over them through chargeback representing.
3. Triangulation fraud
In this fraud, three points are used.
The first is a fake e-commerce storefront that provides highly demanded products at very low prices. The only purpose of the false shop is to collect credit card and address information.
The second point of the triangle is where the fraudster uses other stolen data to make a purchase from a real online shop. They order the goods to be shipped to the initial client.
The final corner involves making additional orders using the stolen data.
At this point, it becomes difficult to connect the order and credit card data. Consequently, an e-commerce store may incur great losses as the owner may not discover the fraud quickly.
The fraud needs robust e-commerce payment security.
4. Phishing/ account take over
It happens when the fraudsters access your online payment services account like PayPal and Apple pay.
In most cases, this hacking is easier since most people use easy-to-guess passwords.
Hackers can easily crack such passwords by collecting a bit of personal information through searching on the web.
5. Card testing
Your e-commerce payment security efforts should be able to take care of this mischievous fraud. It is among those online thefts that are rising very fast.
Online businesses have witnessed up to 200% rise in such fraudsters since 2017.
At first, the thieves usually make smaller orders seeing if the store will smoke them out.Later, they branch into more expensive items until the balance on the card runs out.
If the real owner of the cards initiates a charge-back, the merchant usually incurs great losses.
6. Skimming
Fraudsters may attach plastic devices on credit card readers in gas stations, ATMs and other places.
While you may notice some of these skimmer devices, there are those which are very sophisticated and fit snugly on the card processors.
The aim of the skimmers is to collect your card data via Bluetooth or physically. Always avoid low-traffic areas as they are more vulnerable to such thefts.
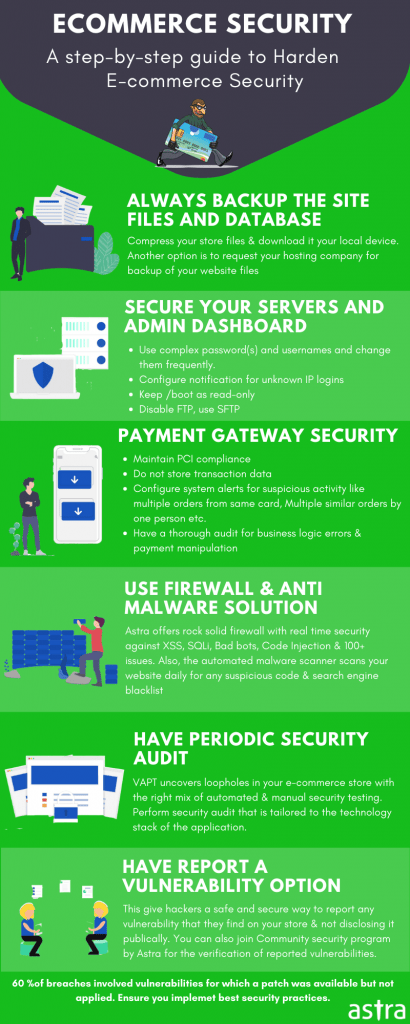
How to Ensure e-commerce Payment Security for your Store
If you study at the statistics surrounding issues around online security, it may come as a shock to you.
Statistics indicate that hackers will attack every 39 seconds. Hackers create an estimated 300,000 new malware every single day.
Here’s how you can secure your online store from hackers and lockout the nasty guys.
1. Partner with a robust online payment processor
Exercise due diligence before settling with a payment processing service.
The experienced and professional partner should offer 24/7 support and maintain PCI compliance through vulnerability assessment and training programs.
2. SSL protocol
Implement the SSL protocol on your website before going live.
It boosts your e-commerce payment security by encrypting credit card information, sensitive customer details, and other crucial data.
Additionally, when customers see the padlock icon in your website URL, they will feel safe and secure. Thus, your reputation will grow.
3. PCI DSS compliance
Payment Card Industry Data Security Standard (PCI DSS) is a set of regulations that popular card brands created to safeguard online payments.
Such brands include Visa, Mastercard, American Express, and JCB.
You need to adhere to their 12 general data security requirements before you store, process, or transmit credit card data.
The sad reality is that more than 63.3% of online e-commerce shops are not PCI DSS compliant.
If you want to avoid the headache that comes with the DCI compliance process, you can partner with a reputable payment processing provider that covers all the PCI issues.
4. Tokenization
It is a technology that enables your store to boost e-commerce payment security and offer a payment process void of vulnerabilities.
In this process, random characters are used instead of the 16-digit credit card number or other sensitive information. These tokens lower data breach because they are useless to fraudsters.
5. 3D secure
You can use 3D (Three Domain) Secure, which is a messaging protocol that adds extra security for card-not-present transactions.
It involves three domains, such as the issuing bank, the payment processing technology, and another bank.
After a buyer initiates a payment, the system will need them to fill biometrics or tokens to confirm the information.
Therefore, it helps in thwarting the thieves’ attempts. Additionally, it transfers the liability on the verified transaction from the trader to the issuing bank.
6. Address verification service (AVS)
It is a tool that helps in checking whether the cardholder has provided the same billing address that appears in the card in question.
The credit card processor sends information to the merchant to let them know whether to accept or reject the transaction at hand.
However, it’s worth noting that the transaction may fail the authentication test, mainly due to misspellings or outdated details.
Additionally, you need to add more e-commerce payment security, as AVS doesn’t guarantee protection.
Conclusion
Online payment frauds are on the rise every day. It is good to stay alert to ensure no e-commerce fraud misses your attention.
Putting in place robust e-commerce payment security is a sure way to beat the thieves at their game. Additionally, partnering with a professional team will go a long way in keeping fraudsters at bay.
Focus all your energy on growing your business as Votz Communications focuses on your e-Commerce payment security.
Love these articles make me happy my sharing.
Related Articles: